The Volume Shadow Copy and System Restore Conundrum
For those users of Windows, there is exists a service that protects your data on a regular basis. This service is called Volume Shadow Copy and runs on every version of Windows post XP SP1. In Windows 8, this service will essentially be renamed File History, but share many of the same underpinnings. The difficulty I speak of, however, is that of the files this service creates, and the ability to make gainful use of them (especially if you don’t have the system to work with).
So, some of the basics to start with. Volume Shadow Copy (or VSS for short) creates most of the files it needs in a folder on the root of each volume. This service generally allows you to restore a system (or some of the system’s files) to an earlier point. The local folder where all this is done is called System Volume Information. There are some things you can do with that folder (and service) to use it and understand it better.
1. Access it – You, by default, don’t have access to this folder, but you can gain access by changing permissions. Microsoft outlines this process in a rather lengthy article, but most of you will use a command like this to open the folder up for use:
cacls “driveletter:System Volume Information” /E /G username:F
Another method is using the handy psexec tool to run a command prompt as system:
psexec -s cmd
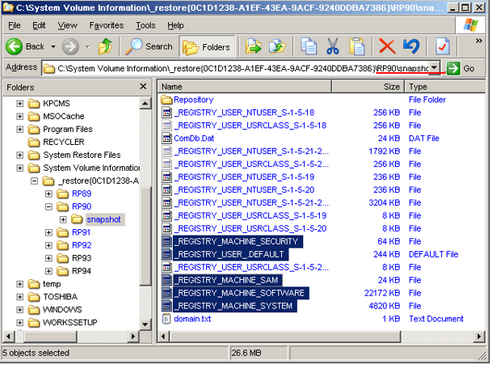
2. Mount various recovery points – If you can access the booted system, there is a utility called System Restore Explorer based on AlphaVSS that has gotten allot of attention from various sites all over the Internet. It’s a small, free and abundantly useful way of gaining a mounted connection to the various restore points you may have on a system.The difficulty starts when you’re attempting to recover files off a failed hard disk. In this case, Windows may not be functioning or the drive may have been partially (or wholly) corrupted. Given that, the files in the computer’s System Volume Information folder may be of use in the process of recovering data.In Windows XP, these files are represented in a raw format. So, you could gain access to them directly and restore them if you needed to. For example, here’s a restore point containing a bunch of registry files.
In Windows Vista (and presumably after Vista), the files take on a different form. Instead of a large base of raw files, restore points are represented as single image files.
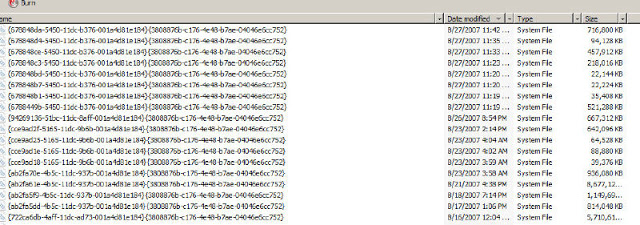
These files are pretty big and will be inaccessible by means other than raw viewing if you don’t have the system they were based on. In the files, you find a reference to the computer name at the start – so it seems that it may be possible to rebuild the system and place these files back to get access – but I think that’s unlikely.When viewing any of the above files – you’ll see that there are actual files in these massive images (for lack of a better word). It doesn’t seem like these files are VHD formatted images either. This would really make sense for later use if a catastrophic failure were to occur.So far, I’ve not been able find a tool to open or extract files found in these images. If you know or have come across something, I’d love to hear from you in the comments.