Don’t Blame the Millennial, Shadow IT loving, Tech Guy
Just like medical journals, it seems like every new day brings some new report or another on the “state” of technology. Some reports are “nothing is secure, and you can never be secure“, while others take a more alarmist “secure everything” approach. I’m always skeptical when I hear of these things. They’re flashy, push people’s buttons, and generally feel like squeeze pages for a larger sales tactic. In fact, the first thing they should disclose is what they sell. At CWL we provide technical support services, so this topic is one that I’m acutely interested in. That said, there are often good things to glean from even the worst.
The full report and risk-mitigation list are behind a registration-wall. Somehow, this is such a common practice that we seem ok with offering personal details to get a report that tells how we’re potentially insecure. That seems rather ironic. Maybe that’s just what you pay to see something that tells you that you need a single sign-on utility.
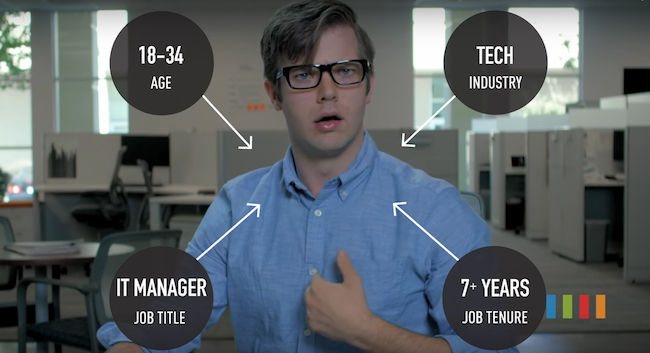
The report looks like a saved Powerpoint presentation. It describes how Millennial IT workers are just about as evil as it gets. They reuse passwords often, are cool with “Shadow IT”, steal your data when they leave and are apparently bad for dropping hard drives off desks. To add to the fear of the Millennial scourge, there are quotes from old people saying things like “Their first experience is that ‘tech = fun’“. How can anyone take stuff like this seriously?
Yes, it seems in the process of trying to be entertaining and edgy, they may have inadvertently insulted an entire generation of IT workers. Ah, but it’s funny, right? The very short run to viral gold is paved with drivel like this.
So let’s be clear: All this report does is describe the very challenging “chicken-and-egg” scenario every small to medium business encounters. Most users and supporters are still trying to find their way in this world of technology options. This should not be a revelation, and, in fact, should signal that things are improving. Overcoming these challenges is difficult and sometimes impossible for smaller businesses. If you are part of a small business, you need a technology provider that eschews the kind of trust you can’t buy.
What does Intermedia suggest companies do to mitigate these risks? You know, beyond buying their products.
- “Create a central repository for admin logins and passwords.”
This is a good recommendation and can be achieved by using a Keepass database with all the company’s many logins and passwords. Make sure there are backups and hard copies of these details exist. - “Control access to hardware and track IT activity with a ticket system.”
For smaller companies, ticketing and asset management systems can be far too unruly. If you want to keep it simple, but enjoy these benefits, consider using something like the free Spiceworks‘ hardware scanning capabilities, coupled with good, simple incident reporting with your favourite word processor. - “Eliminate shared logins/accounts.”
Reasonable, yes. But for some small outfits, impossible. Look to take a sane, clear set of steps that take your users away from shared network logins and work/personal shared accounts. If you started small, many of these will mix but have those in IT take daily steps to get you there. - “Conduct regular audits.”
Generally the “cleaning the grout” part of IT. Most small companies don’t even consider this. To improve your knowledge on what needs to go, make cleaning accounts and information a part of a user’s exit. Don’t just disable the account and move on, clean up what he/she had access to, and remove those credentials. - “Check access logs to critical systems frequently.”
A good suggestion, but an extreme challenge for a small growing business. In the place of this, your IT support person (or company) should educate you in what’s going on. Look to him/her to give you the tools to understand your systems and navigate challenges.
Many of these recommendations are common-sense but too big for a small company. But, for every big weekly audit, you can gain most of those benefits by scaling back some of the tools and approaches. The most valuable thing anyone that supports your systems can do is to find what’s right for your company and make IT work.
What about CWL? As an I.T. and technology provider, we follow some very “no – bull” practices that should ease your mind.
- We’re professional. We handle everything about your business with respect.
- We want you involved and educated. We’re here to help you understand what systems you run. We provide a full systems documentation package and update it regularly. There is nothing you don’t know about how things work. All our invoices include detailed reports so you know everything that happened.
- We trust you. We’ll recommend the best course of action, but we would rather you get what you want than tell you how wrong you are. It is more important to find solutions.
- We’re tireless. When a solution requires an all-night effort, we’ll be the first in and the last out the door.
Every single client operates differently and has different systems. For more than 15 years in business, we’ve learned to mould our efforts to your company’s needs, not our view of what technology should be.