Bemoaning The Abrupt End Of TrueCrypt
If you’ve been following news about security and encryption tools, no doubt you’ve heard of the shutdown of popular open source encryption tool TrueCrypt. Given that using TrueCrypt was considered one of a handful of ways for individuals to protect data in the wake of recent NSA spying revelations, this unexpected news has rocked the Internet. I’ve been waiting for more details to surface from developer about the shutdown, but things are far too silent for my liking. I thought I’d take a look at what happened, what’s out there and whether we should all abandon TrueCrypt altogether.
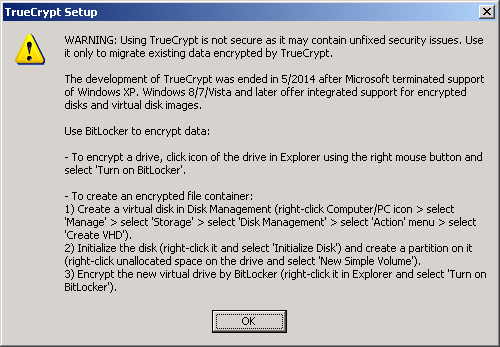
As you may now know, hitting the TrueCrypt website places you on SourceForge and presents you with the seriously ominous message:
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
This is followed by a short description of how to create encrypted containers on Windows, OS X and Linux with alternate tools. At the bottom of the page, you’ll still find links to download a 7.2 version of the tool (updated May 28th, 2014). They make it clear that the version offered is intended for “data migration” to another encryption tool, and not general use. If you install it and try creating an encrypted container, you’ll see a message that repeats most of the SourceForge page’s swan song. TrueCrypt 7.2 does not let you create new encrypted containers, just read from old ones. In addition, the SourceForge page no longer includes older TrueCrypt editions.
Given the unexpected nature of this shutdown, many are wondering the real story behind TrueCrypt, and what lead the authors to such a drastic step. Typical of unexpected shut downs, speculation runs wild about why. Here are some of the more popular theories.
– Actual coercion or intervention by government officials
– A means of signalling Government interference (a possible Warrant Canary)
– Some kind of internal squabbling
– Killing the project before a possible backdoor discovery by researchers
– A Dead Man’s Switch, the change was pushed based on some external pressure (or accidentally)
– The developers lost interest
– Wishing to remain anonymous, the current climate (Snowden/NSA) would not allow for that
– A very sophisticated hack of some kind (based on gathered evidence, not likely true)
With something this abrupt, it may be a combination of all (or some) of those reasons. The pressure to maintain something so culturally significant must have weighed heavily on the developers. What’s more, the conspiracy theories are fuelled by a number of inconsistencies. Why would those at TrueCrypt recommend an obviously inferior (and apparently backdoored by the NSA) like Bitlocker? Why remove older versions? Why change the license terms? Why offer so little in the way of explanation?
The beauty of open source, and openness in general is that something good out there can live on in other forms (if the people want it). In the case of TrueCrypt, the demand for such an important encryption tool motivated a large-scale audit of the tool with more than $46,000 invested it an Indigogo campaign. Currently, the folks at @OpenCryptoAudit are in the middle of auditing that last fully working version of TrueCrypt (7.1a). At this point in the audit, no vulnerabilities have been discovered.
Currently, version 7.2 of TrueCrypt should not be downloaded or used. If you want to continue using the tool, look for the 7.1a version from a number of mirrors. It also appears as though we’re on the cusp of seeing a viable encryption alternative that might fill this void. But, should we be quick to abandon TrueCrypt?
No. As it stands, TrueCrypt 7.1a is still widely available on the Internet, safe, and generally good to use on all supported operating systems. We may never know why the developers decided to leave such an important project, but this doesn’t mean you can’t continue to use this tool to encrypt your data for the foreseeable future (1). What will be interesting is the results from the current audit. Could this all have been foreshadowing a larger problem yet to be revealed?
Update: In probably one of the most bizarre and fishy theories you’ll find can be found on popular text posting site Pastebin. The author of this short text describes TrueCrypt’s ominous website warning as a message in latin. The translation roughly reads “If I wish to use the NSA”. Not exactly the most conclusive, if not weird, message ever.


