Fixing ScreenConnect Two-factor (2FA) Login Failures
This one’s a real pain because of how little information is out there. For what I describe below, I’m basing it on an installation of a Hosted Screenconect (Connectwise Control) version 20.9.799.7542 on a domain-joined Windows Server 2016. Your mileage may vary, but the fundamentals of this issue should hold across servers and platforms.
Know that just about a minute is enough to throw off the server’s two-factor authentication and block all users from accessing the server.
Here’s what I did. You also want to create an isolated environment between the authenticator device and the server.
- Focus on the time on your server and on the authenticator device. If they’re even off by a minute, make sure they are the same; even if you have to set them manually. You’ll want to update to world time servers but can start by simply getting them as close as possible to test.
Additionally, if you’re in Windows – using commands like w32tm /resync and for domain-joined servers: net time /domain – making sure any time synchronization isn’t going to mess you up. - Restart Google Authenticator on the device and your Screenconnect server.
- Test another login.
- Iterate through this process making sure the times are closer.
Some other things to keep in mind
You want to have a login to your server that can be used without two-factor enabled. If you’re locked out due to time, yes you’re out of luck, but when the server comes back, set this up. This account might be your admin-type login, but make sure it has an insanely complicated password. This will allow you access to the system in the case of two-factor failure. Time clocks are not going to stay in sync forever.
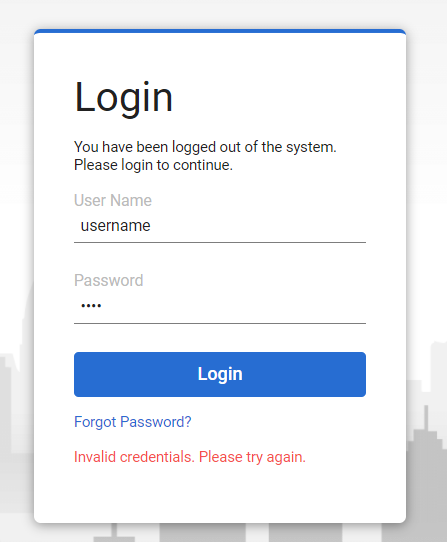
ScreenConnect is also not going to tell you what’s going on. You’ll get login failures with no idea. On the server end, Screenconnect provides no information on time, how the two-factor process operates or logging information in that regard. Don’t look at the software to provide clues. Hopefully, that changes in the future.
Also, it would be a good idea to get ScreenConnect’s email abilities working (if you haven’t). This may provide an alternative second path to getting 2FA working in lieu of fixing the problem.
Keep at it, everyone. Let me know if you’ve encountered this yourself.

