This year’s iPhone upgrade was significantly different for me. On the same day as pre-ordering Apple’s newest phone, I prepared and sold my current iPhone 12 pro Max. This effort would retain the maximum value for the 12, but also require me to endure the use of an iPhone 7 for a week. Once a […]
For those who act on the need to dump words into something resembling a book, they’ll be pen-to-paper purists or the type that I am: write it all out on a computer. Certainly, there are other options, but why in the hell would anyone type out a book using Dropbox and a smartphone? What I […]
The moment all this sunk in (see part 1), I felt a keen sense of desperation and finality. As someone who works in technology and is considered an expert by many – I felt a distinct sense of shame. How could I have let this happen? How could I have let them fool me? Coupled with my already careful nature, I’ve bought and sold online for more than a decade. It shouldn’t have happened. After allowing that feeling to marinate, I set out to investigate. I had to learn more and maybe catch these culprits.
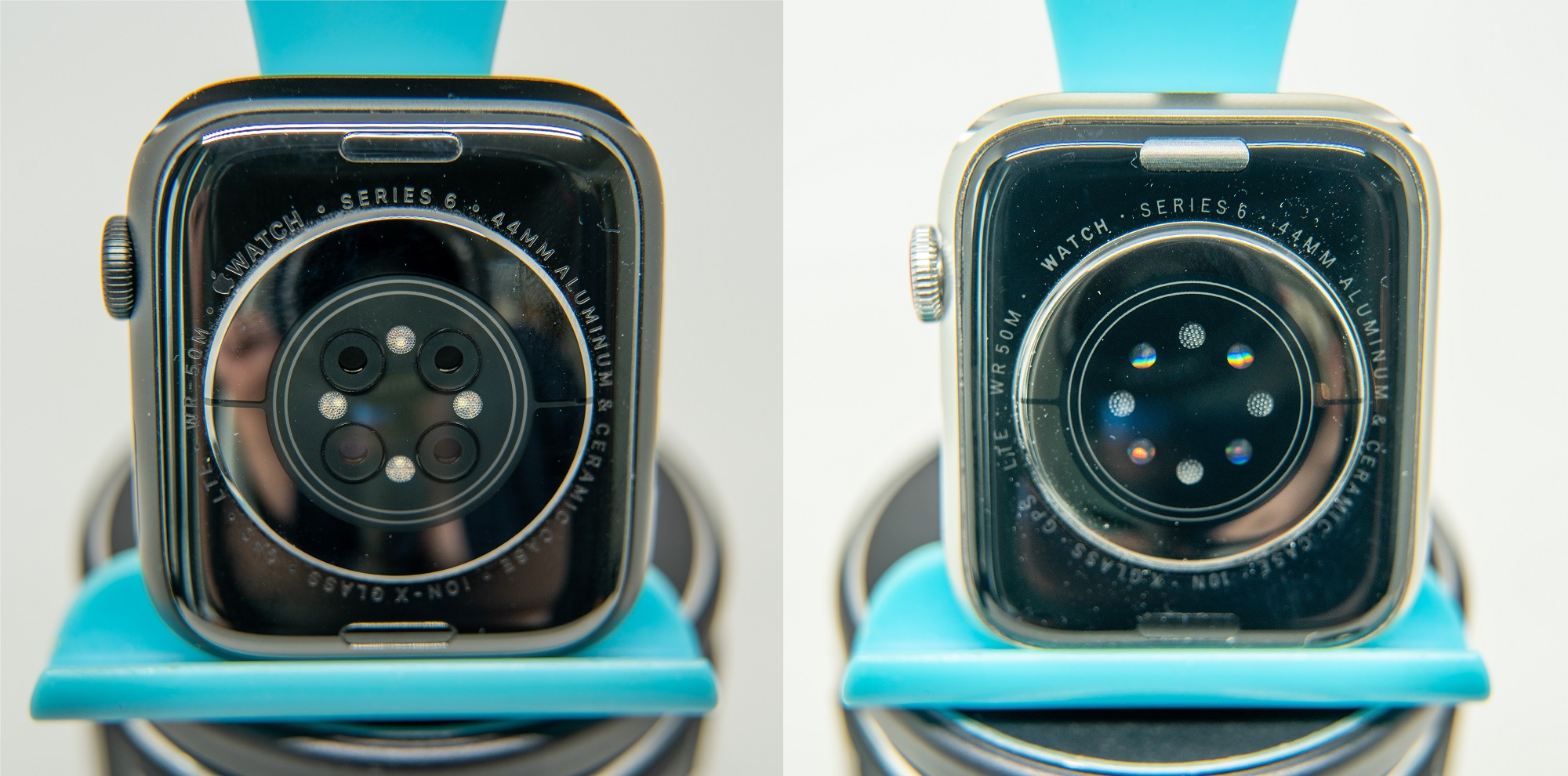
Can you spot a fake? This week I learned the hard way how difficult this is. Using Kijiji – an online marketplace considered a ‘grey market’ for new and used physical items – I bought a brand new Apple Watch Series 6. This Watch was posted as new and sealed in the box for $450.00, a price I haggled down to $420.00. The practice of selling close Apple Watches is common, but the work made to present this product as new and legitimate is unique. I investigated this phenomenon while ending up with two excellent duplicates, $420.00 poorer and in a confrontation with a scammer.
I have some new, free, software for you. It’s been a while since I’ve released anything new – years in fact. This time around, I’ve made something to help with the laborious task of calculating taxes on a final amount. This comes up in situations where the receipt a company gives you doesn’t include a […]
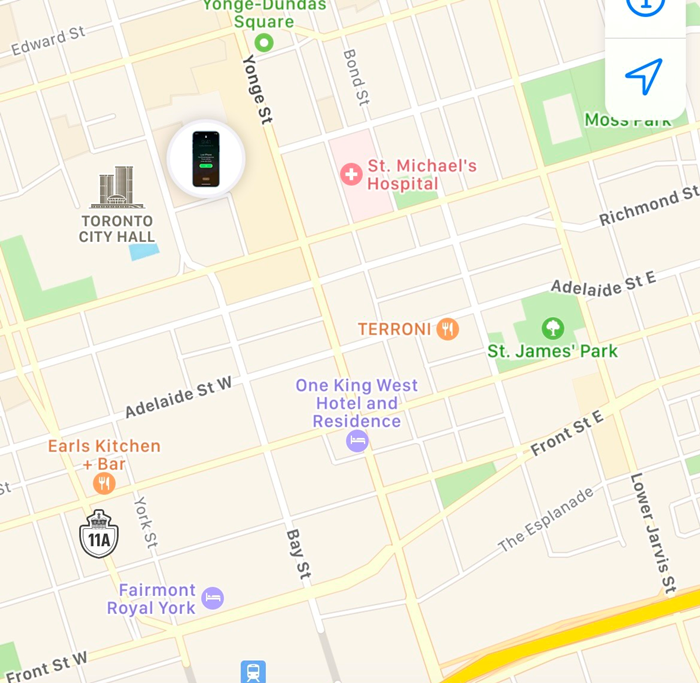
Smartphones are devices that rule our lives. They now cost more than a mortgage payment to purchase. They hold everything important to us. They’ve become so fundamental to everything we do. When we lose one, it can feel like we’ve lost an appendage. This summer, I left my phone behind at a park and it […]
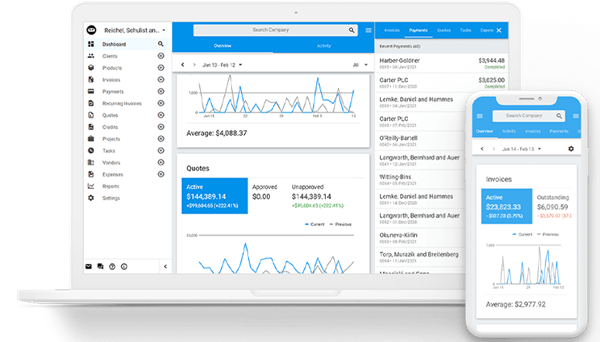
It’s been a whirlwind year working with InvoiceNinja 5, a web-based accounting package you can run in the cloud, or on your own server (self-hosting). Think of it as Freshbooks, but running on your own servers. I’ve run through self-hosting every version available, testing with dummy data, pulling out my hair, migrating from Quickbooks and […]
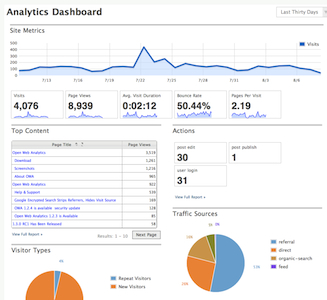
Here’s the problem: I want to use Open Web Analytics (OWA), but I want to install it in a Docker container. With no official Docker image to draw from, I’m left with poorly maintained alternatives. In this article, I’ll take you through how you might use an older docker image, update it and get the […]
Tile, Apple’s direct product competition, makes a more mature product with more sizes and more market share. Apple is probably going to do what it’s done a number of times before: Arrive on the scene with an “okay” product and completely decimate the competition. With tight integration into iOS, name recognition, pent-up demand for Apple-branded newness, and just an Apple high right now, expect AirTags to be a winner. Tile is going to have more features, call Apple anti-competitive, team up with others while fighting the good fight.
Simon Freedman returns with an email message. It’s clearly an apology, but there’s more going on that I’d like to look at closer.