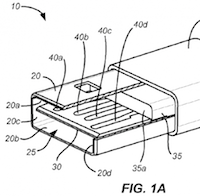
I take a quick and dirty look at reversible USB lightning cables. Interest in these simple cables is at an all-time high with a possible Apple announcement.
Let me help keep you out of IT prison. I offer 10 phrases you shouldn’t be saying to your (or any IT person. You’re welcome.
Just looking at the numbers, the proposed Tim Hortons/Burger King merger might look great. But, there is more to this story, and I explain why this might be a bad idea.
I take a first look at Emojli, the first emoji-only chat service and look for someone to chat with.
News of a Canadian-ISP-backed Netflix rival Shomi has people talking. But, are they talking about what’s important? I look at some concerns about this new service.
Yesterday I was hit with an idea. I present you with the app application description for “Runner” – a crowd-sourced micro task tool that anyone can use to get what they want or make money helping others.
A newly revamped Bittorrent Sync arrives with new features and a new interface. The tool is working to appeal to less technically savvy users, and this update should go a long way in that regard.
I talk about whether it makes sense to move to HTTPS, even if your site doesn’t sell products or take in user data.
ScreenConnect, a remote access tool, allows you to host a server that enables remote support of client computers. Many of the best features of this software relate to giving you control over deployment and hosting. This would seem like the perfect fit for Amazon’s cloud server infrastructure. If what you wanted to do is run it on a lower-cost AMI (Amazon Machine Image) free-tier micro instance, here’s how to do that.
I’m reminded of a rather prescient article from Kurt Sutter – creator and showrunner for Sons of Anarchy. I consider him eloquent, interesting, entertaining, and somewhat crazy. But he’s also as wrong as, well, everything Gene Simmons says. The early August article for Variety went after Google and its apparent love of piracy.